U.S. customers who have previously used Sweden-based Klarna's buy now/pay later financing — and paid off their loans in full — will be prequalified for interest-bearing loans through a new version of the Klarna Visa card rolling out later this year.
-
To help historic restaurants facing dramatic losses when COVID struck, American Express rolled out grants to 25 needy restaurateurs. Four years later, the program is reaching twice as many establishments and the card network's investment has more than doubled.
April 8 -
A digital-payment trend that began during the COVID pandemic is being bolstered by features such as rewards and state ID storage.
April 5 -
-
The credit and debit card-issuing giant's Chase Media Solutions will help fund new loyalty programs to offset downward pressure on card-swipe fees and the potential erosion of card spending volume from the rise of faster payments and open banking, experts say.
April 4 -
Visa is working with Thunes; LemFi and Western Union to expand its reach; Swift has completed testing of 38 global digital currencies, and more.
April 3
American Banker's Most Influential Women in Payments share their views on artificial intelligence, hybrid offices, real-time payments and more.
Honorees from 2024's Most Influential Women in Payments, representing companies such as MoneyGram, Walmart, Segpay and more, share insights into how how artificial intelligence is changing their companies and their industry.
-
Ambitious women who feel trapped in their roles sometimes find themselves competing against others with the same goals. An effective way to advance may require stepping off the most obvious path, according to executives sharing their personal experiences at American Banker's Payments Forum.
April 2 -
The bank is launching KeyVAM, a virtual account management offering it designed with fintech Qolo. Both companies said the nature of the relationship was as important as the technology it produced.
March 28 -
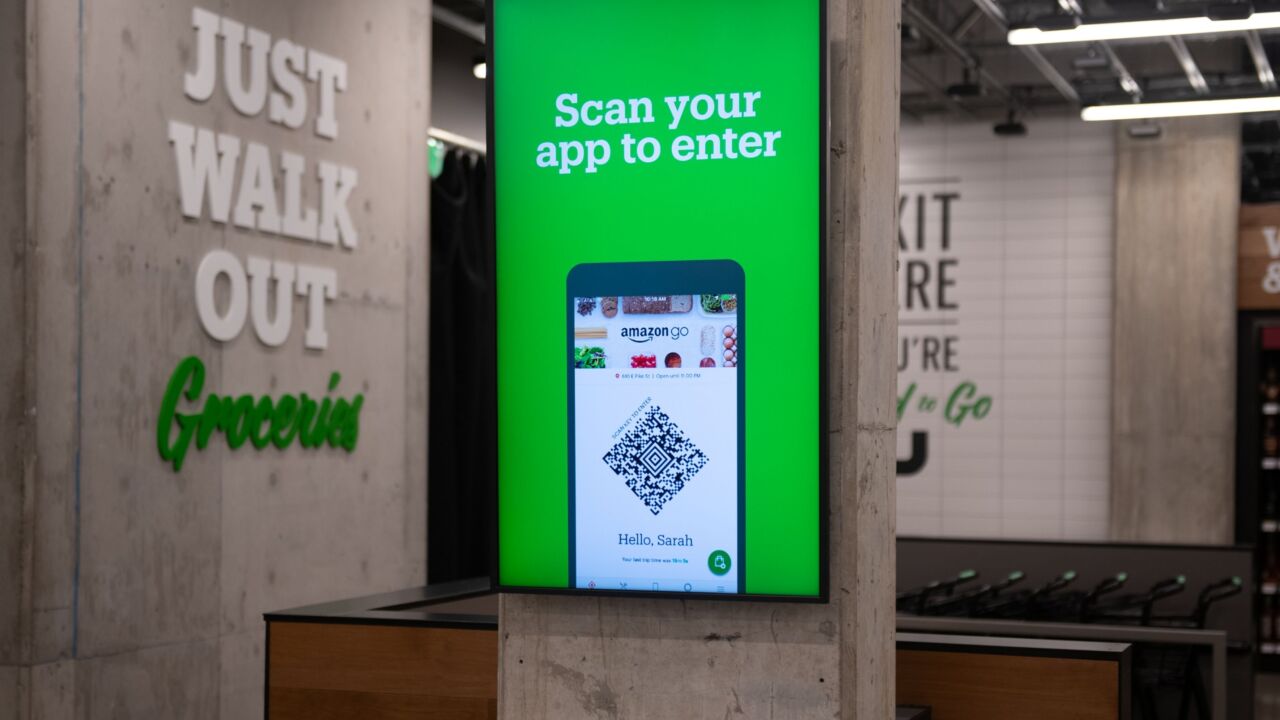
Amazon is working with Stripe to expand its Just Walk Out retail stores in Australia and Canada; Safaricom is working with Onafriq to support remittances sent via M-Pesa to Ethiopia; and more.
March 27 -
A new crop of AI-powered products from Visa tackles scams beyond the company's network to include account-to-account payments and digital wallets.
March 27 -
Despite further delays, the country has taken two key steps to opening up access to its Real-Time Rail, including allowing payment companies to participate without a bank partner, but it has yet to commit to a date for the project to go live.
March 25