Companies are taking vastly different approaches to how they implement generative AI, whether it's to empower employees or to overhaul the way they bring products to market.
-
Ambitious women who feel trapped in their roles sometimes find themselves competing against others with the same goals. An effective way to advance may require stepping off the most obvious path, according to executives sharing their personal experiences at American Banker's Payments Forum.
April 2 -
The bank is launching KeyVAM, a virtual account management offering it designed with fintech Qolo. Both companies said the nature of the relationship was as important as the technology it produced.
March 28 -
-
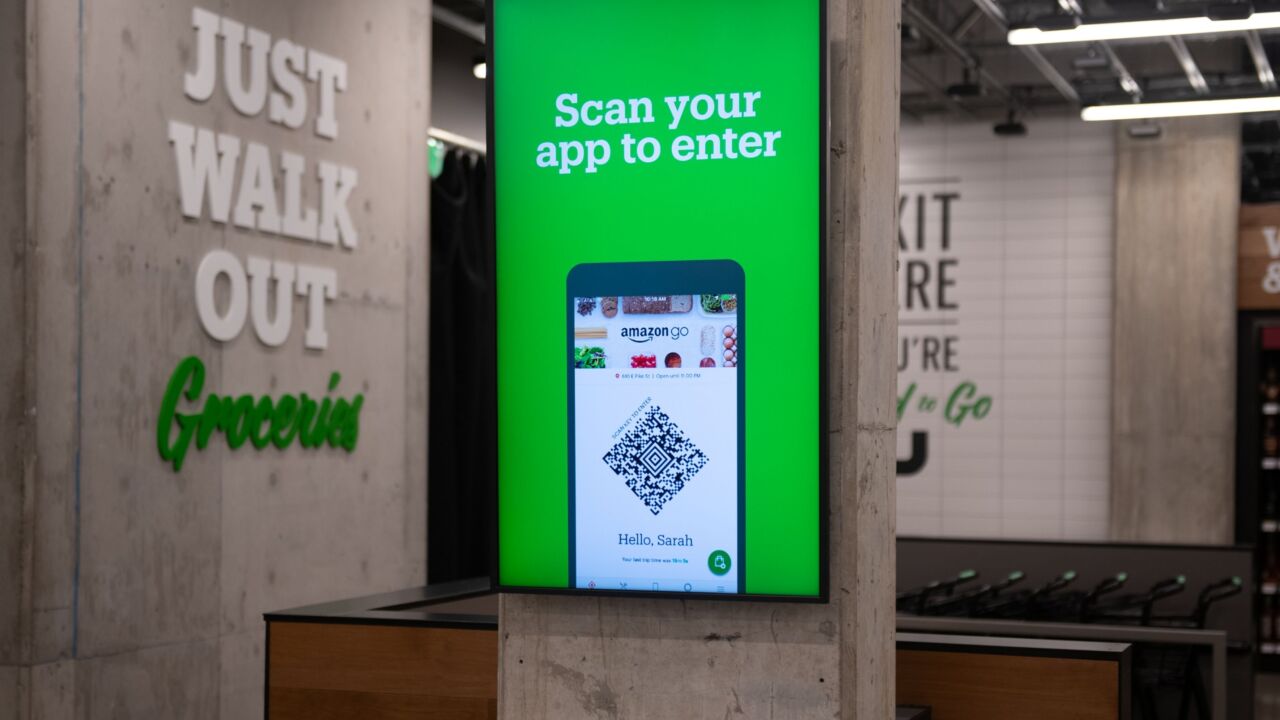
Amazon is working with Stripe to expand its Just Walk Out retail stores in Australia and Canada; Safaricom is working with Onafriq to support remittances sent via M-Pesa to Ethiopia; and more.
March 27 -
A new crop of AI-powered products from Visa tackles scams beyond the company's network to include account-to-account payments and digital wallets.
March 27
American Banker's Most Influential Women in Payments share their views on artificial intelligence, hybrid offices, real-time payments and more.
Honorees from 2024's Most Influential Women in Payments, representing companies such as MoneyGram, Walmart, Segpay and more, share insights into how how artificial intelligence is changing their companies and their industry.
-
Despite further delays, the country has taken two key steps to opening up access to its Real-Time Rail, including allowing payment companies to participate without a bank partner, but it has yet to commit to a date for the project to go live.
March 25 -
The launch of Apple Pay a decade ago set the tone for how the tech giant would interact with banks and credit unions in the years to come. The Justice Department is now pushing back.
March 22 -
Criminals who buy and sell consumer data on the dark web are perpetrating increasingly complex credit and debit card fraud schemes, according to the card network's latest threats report.
March 21 -
The U.S. Justice Department and 16 attorneys general sued Apple Thursday, accusing the iPhone maker of violating antitrust laws by blocking rivals from accessing hardware and software for digital wallets and other features.
March 21 -
The fast-food chain is analyzing the cause of an issue that affected payments in multiple countries. Separately, dLocal, a payments processor in Uraguay, is making changes at the top.
March 20